The Go-Bag
The in-house team I work with are in the process of updating our digital forensics go-bag. While it is not common for us to perform field collections, the go-bag will enable us to arrive on-site equipped without needing to stop by the office before hand. Our goal for this updated kit is to balance capability, flexibility, and cost. We have the benefit of knowing what to expect and have appropriate privileges to perform a task, so we also expect the kit to be compact.
After reviewing a handful of resources, our go-bag list included the following ordinary items:
- Flashlight and extra batteries
- Anti-static bags
- Faraday bag
- Screw driver kit
- Portable battery with USB
- Sticky notes
- Markers
- 1″ masking tape
- Scissor/utility blade
- Storage media with tools
How about write blocking capability?
Write Blocker Notes
For an on-site collection, we expect to encounter various storage and interface types: SATA, IDE, M.2 SATA, mSATA, USB, and NVMe. As Bruce Nikkel mentioned in his paper, “NVM Express Drives and Digital Forensics“, forensic techniques for many of these storage types are well known and tested. However, it seemed M.2 NVMe SSDs require more thought. Write blocking NVMe SSDs is still relatively new. When Nikkel’s book, Practical Forensic Imaging, was published in 2016, the Tableau T7u was the only dedicated hardware write blocker available. In 2021, WiebeTech’s NVMe WriteBlocker was introduced.
I created a matrix of different storage and interface types we’re likely to encounter, and the write blockers and adapters capable of imaging them.
| SATA | USB Media | M.2 NVMe PCIe | M.2 SATA/mSATA | Compatible Software | |
|---|---|---|---|---|---|
| Bootable Media, like WinFE | N/A | N/A | N/A | N/A | N/A |
| ForensicSoft SAFE Block | Adapter, Inateck w/ASMedia | N/A | Adapter, JMicron JMS583 | TDA3-3 or DI A4710 that will connect to a USB to SATA/IDE adapter. | SAFE Block |
| DeepSpar Guardonix Professional, USB 3.0 | Adapter, Inateck w/ASMedia | N/A | Adapter, JMicron JMS583 | TDA3-3 or DI A4710 that will connect to the Guardonix. | Guardonix Control Panel |
| WiebeTech | UltraDock v6, USB 3.2 Gen2 | USB 3.1 WriteBlocker, USB 3.2 Gen 2 | NVMe WriteBlocker, USB 3.2 Gen2 | TDA3-3 or DI A4710 may connect to the FUDv6. | Forensic Software Utility |
| Tableau | SATA/IDE Bridge, USB 3.0 | USB 3.0 Bridge | PCIe Bridge and M.2 PCIe adapter, USB 3.0 | TDA3-3 or DI A4710 may connect to the SATA/IDE bridge | Tableau Imager |
| Tableau | TC4-8-R3 | NA | TX1 with M.2 PCIe adapter | TDA3-3 or DI A4710 may connect to the TX1 via TC4-8-R3 | Tableau Imager |
Bootable media, like WinFE, is attractive because it only requires my time to set it up and it’s flexible. While it may not address a handful of scenarios, bootable media is simple enough that we will add that capability to the go-bag anyway.
ForensicSoft’s SAFE Block is a lightweight, and capable option. ForensicSoft highly recommends installing SAFE Block on Windows LTSC. If our team used dedicated laptops for field collections, SAFE Block would be considered.
SAFE Block provides automatic write blocking of every directly attached flash and disk media, attached with any interface, including IDE (PATA & SATA), SCSI, FC, SAS, M.2, NVMe, USB, USB-C and IEEE1394.
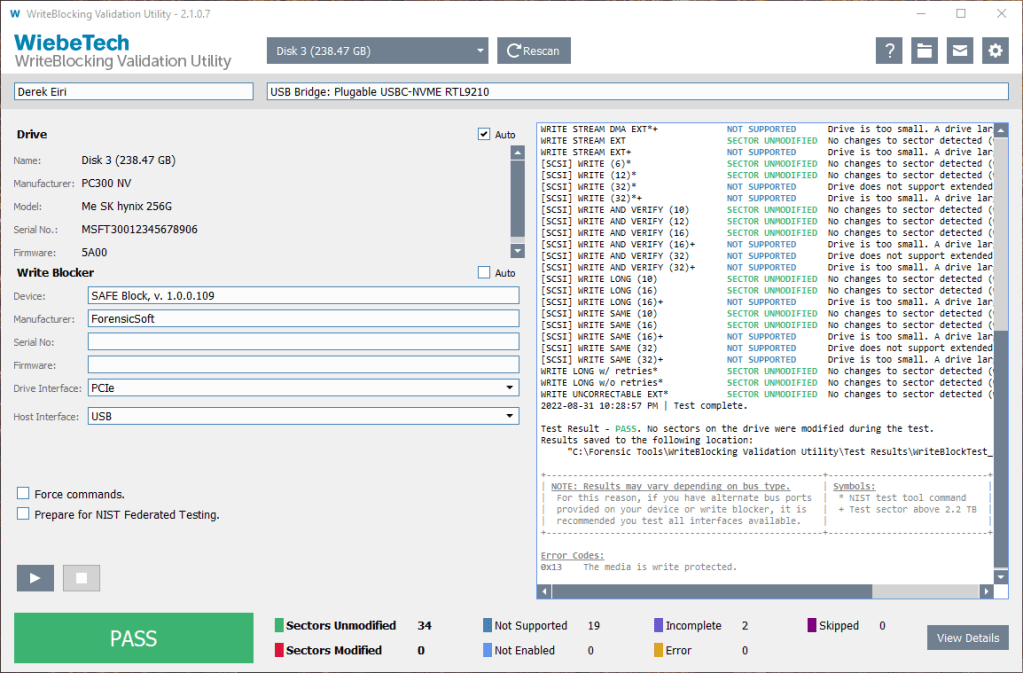
From episode 121 of Kevin Rippa’s 3MINMAX series, I learned about WiebeTech’s WriteBlocking Validation Utility. Putting what I watched into practice, I created a baseline to use on a couple write blockers I have.
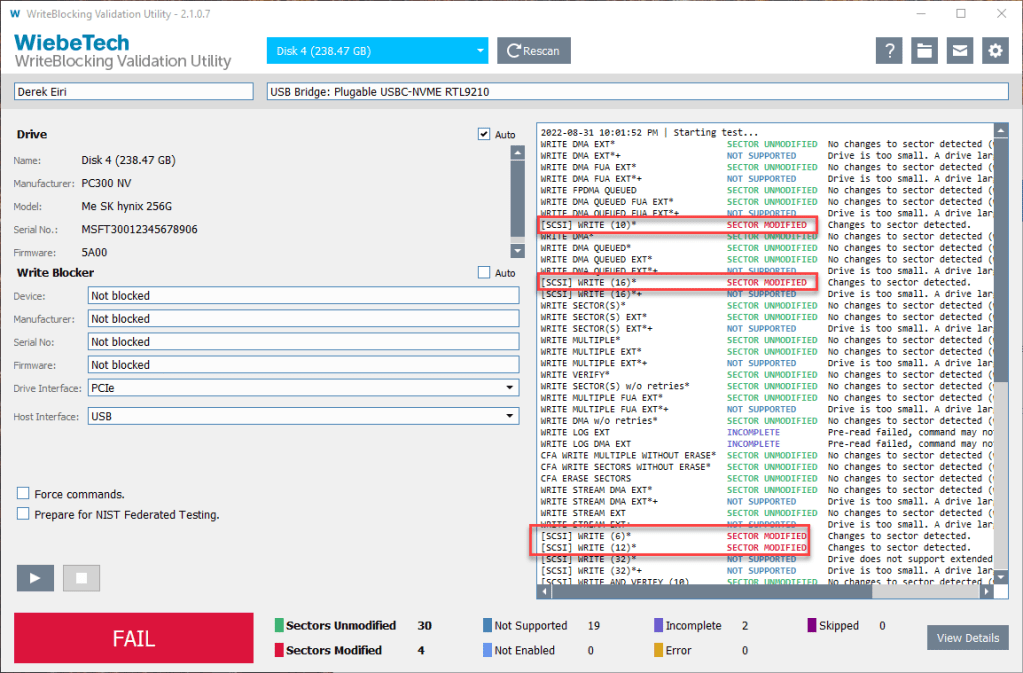
The baseline test on an SK hynix NVMe SSD resulted in 4 modified sectors from 4 commands:
- [SCSI] WRITE (10)
- [SCSI] WRITE (16)
- [SCSI] WRITE (6)
- [SCSI] WRITE (12)
SAFE Block prevented the 4 write commands to the SSD.

At no fault of SAFE Block, I experienced stability issues attributed to a USB cable on my initial tests. X-Ways Forensics and FTK Imager, were able to initiate the imaging process of the NVMe SSD; however, it was notably slow – about 2 GB/min. The drive’s connection also seemed to disconnect intermittently. With ForensicSoft’s help and guidance, I switched out the USB-A to USB-C cable that connects the forensic workstation and the adapter for another. For good measure, I upgraded to the most recent firmware for the JMicron chip in the enclosure. After the switch, I was able to acquire an image at approximately 350 MB/s. Neat! This was a good reminder to ensure the connections between the evidence drive and the USB controller on the forensic workstation are compatible. It also highlights the importance of testing and validating tools in all intended configurations.
- USB controller of the forensic workstation’s USB port.
- USB cable.
- USB controller of the adapter.
- Validating compatibility of adapters downstream, i.e., mSATA and M.2 SATA
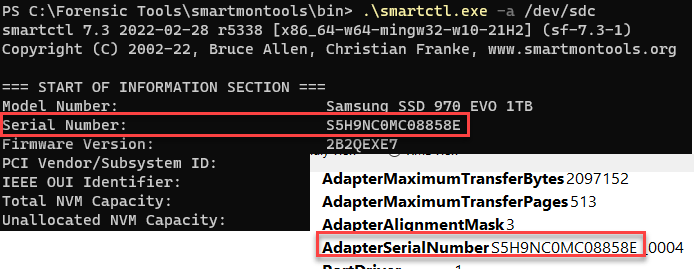
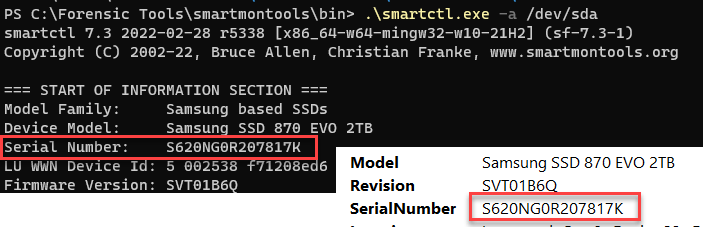
Note: SAFE Block tests with SATA or M.2 NVMe SSDs via USB adapters presented serial numbers that were not of the drive. ForensicSoft states SAFE Block fully supports all ATA and SCSI commands, to include all pass-through commands. This may mean I need to identify a tool that will.
A hardware write-blocker like the DeepSpar’s Guardonix Professional is available, too.
The Guardonix Professional is an attractive option to me for many reasons:
- Compact and lightweight
- Additional functionality with the Professional firmware upgrade: speed optimization, USB connection stability, and keyword searching
- If purchased, the adapters provided work.
- One unit may image the all storage and interface types we expect.
You can read reviews about the Guardonix from Brett Shavers and Marcos.
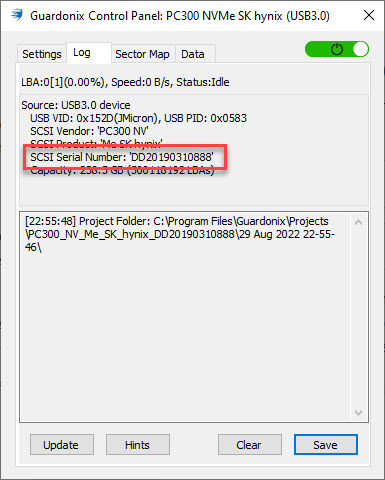
The Guardonix also prevented the 4 write commands to the SSD.
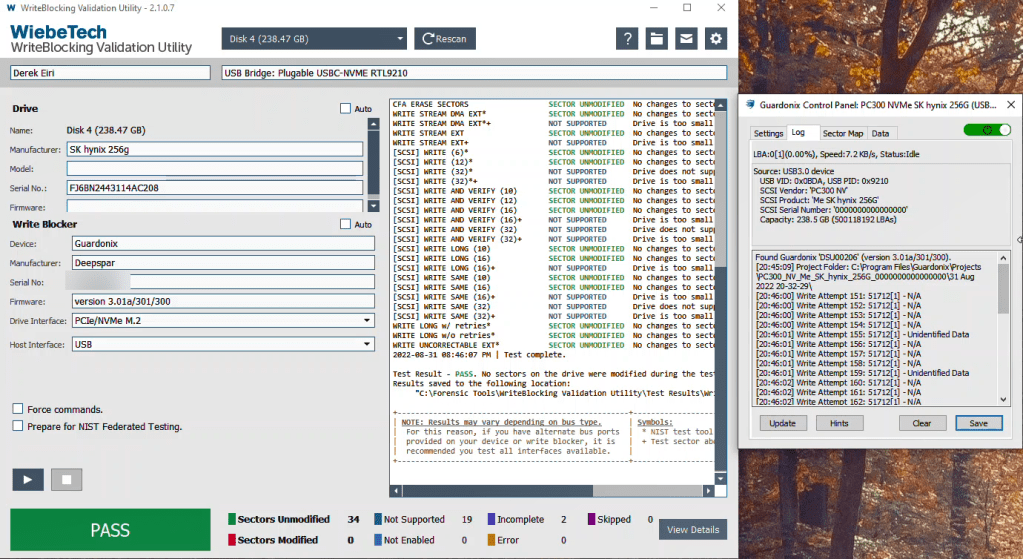
The Guardonix Professional is capable of reporting ATA information and SMART attributes for SATA drives, including the drive’s serial number. It is not, however, able to report for M.2 NVMe drives. Why? I’m not absolutely sure, but I’ve been taking the time to explore it.
Thanks again to Nikkle’s paper and book, Practical Forensic Imaging, I learned a little more about SATA and NVMe drives, and their respective command sets. I also learned that the role of the USB bridge’s chip within an enclosure plays a critical role to translate SCSI commands to either ATA or NVMe commands to properly access SMART functionality (smartmontools, Re: USB devices). Anything between the evidence drive and the forensic workstation would also need to support the translation of these commands – including any write blockers.
No guarantees, but Serge Shirobokov and the team at DeepSpar will take a look at adding support for the RTL9210 bridge so the Guardonix control panel will show the correct serial number for M.2 NVMe SSDs.
What about the other write blockers?
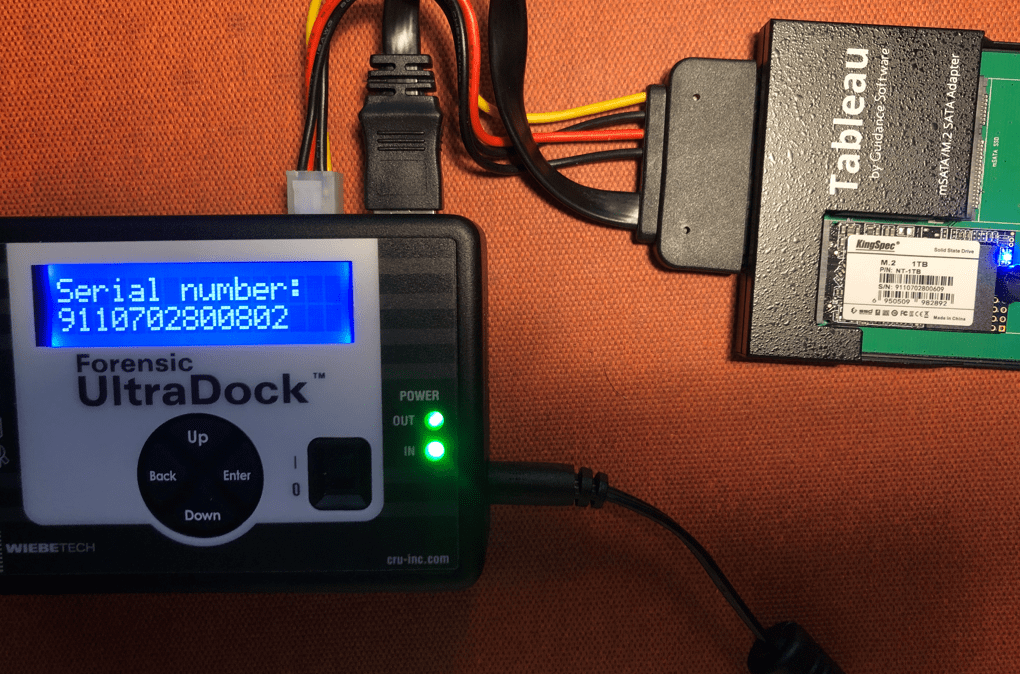
The WiebeTechs, Tableau bridges, and the Tableau TX1 appear capable. For each storage and interface type, the WiebeTech and Tableau bridges are independent hardware that may use adapters and cables, as needed. This may be helpful if multiple drives with different interface types need to be imaged simultaneously. The TX1 is single unit – with the appropriate adapters, this would satisfy all the anticipated storage and interface types. With exception of the WiebeTech USB unit, all are able to provide some drive information on the unit’s display.
I believe WiebeTech and Tablau’s support software is able to extend that ability in a GUI. I know the ForensicDock v.5.5 is supported in the Forensic Software Utility (FSU) to display drive information. As of 08/30/2022, CRU is working on a firmware updater for the v6 and NVME docks. Shortly after, they may switch to the FSU. No definite timeline for this update, however.
The WiebeTech docks and Tableau bridges might be practical for our purpose, but a TX1 imager for each go-bag is certainly not.
Write Blocker Imaging Speed
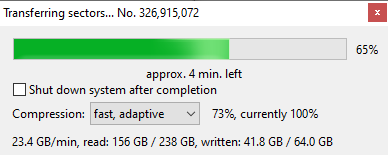
For write blockers I own or have a trial license for, I ran some casual* experiments to assess potential speed. I used a Lenovo M90q Tiny with an Intel(R) Core(TM) i9-10900 CPU @ 2.80GHz 2.81 GHz and 64 GB RAM. The operating system is Windows 10 Pro, 21H2 19044.1889. The hardware write blockers were connected to an Intel USB 3.2 gen 2 10Gbit controller. For SAFE Block, the enclosure was directly connected to the USB controller. The destination drive I used a Samsung 970 EVO 1TB NVMe SSD.
Casual: I initiated imaging (fast, adaptive) with X-Ways Forensics 20.6 SR-1 and let the process run for about 5 minutes, then aborted it. I was curious how hot the NVMe SSDs would get, so only those drives were imaged completely.
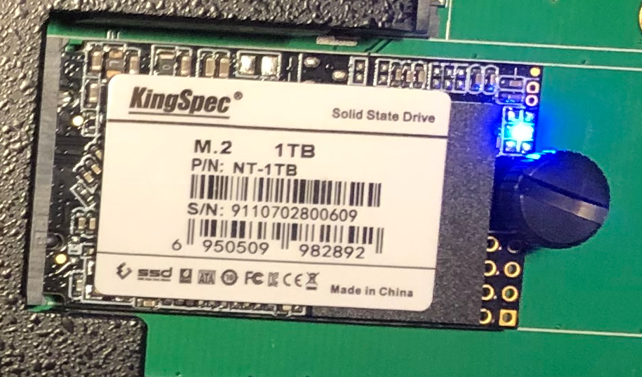
| Kingspec NT-1TB M.2 SATA 1TB 2242 with an Inateck SATA to USB adapter + TDA3-3 | WD WD3200BPVT 320GB HDD with an Inateck SATA to USB adapter. | PM981 NVMe Samsung 250 GB with USB to NVMe enclosure, JMicron JMS583 chip. | |
| Forensic Dock v5.5 | 9.9 GB/min | 4.3 GB/min | NA |
| SAFE Block | 14.6 GB/min | 4.3 GB/min | 20.7 GB/min |
| Guardonix Pro | 23 GB/min, Aggressive* | 4.3 GB/min | 23.1 GB/min, Aggressive* |
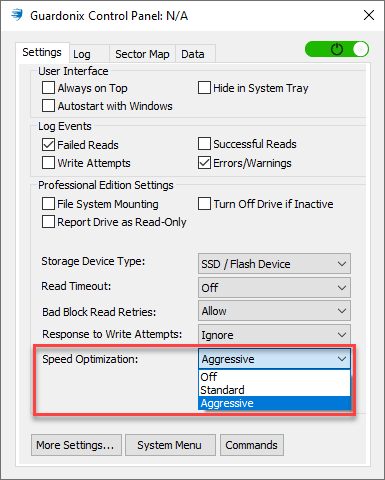
With Guardonix Professional, speed optimization settings may be selected for SSD media. Aggressive may be an appropriate option for healthy drives if you can afford the CPU load.

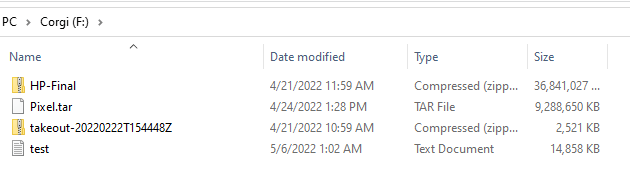
I ran another test using the Plugable USBC-NVME enclosure using the RTL9210 chip. I copied the Magnet Summit 2022 online CTF images on the same PM981 NVMe Samsung 256GB SSD. The speed difference observed is negligible, but I like the tool-free Plugable enclosure a lot more!
I imagine the current version of the ForensicDock (v6) and the NVMe WriteBlocker also have impressive speeds. Both units have USB 3.2 Gen 2 Type-C host ports.
Write Blockers and “Serial Numbers”
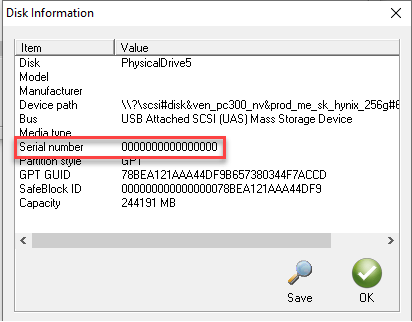
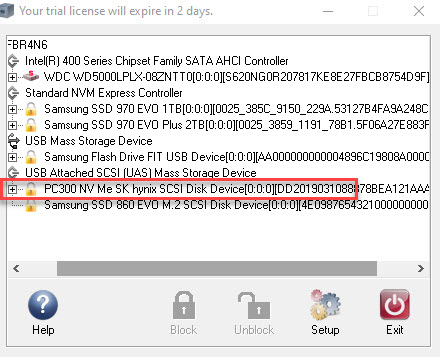
As previously mentioned, I noted the serial numbers of the NVMe SSDs presented by Guardonix Professional and SAFE Block. The SCSI serial numbers reported were not of the drives.
With SSDs in enclosures used for a variety of common purposes reporting different numbers than the serial number labeled on the drive, how might other artifacts on Windows machine be linked to the drive? Yet another tunnel in Kevin Rippa’s serial number rabbit hole to potentially explore.
A demonstration: The Guardonix Professional reported zeros for the serial number of a Plugable USB to NVMe enclosure with an RTL9210 chip.
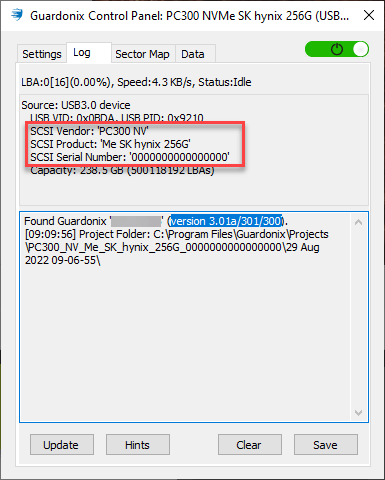
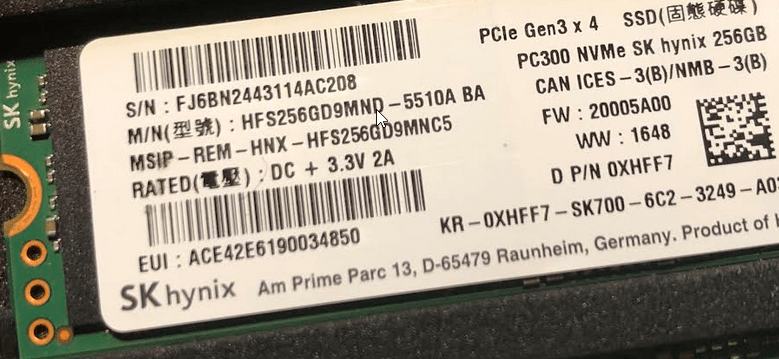
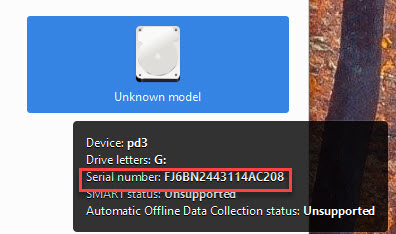
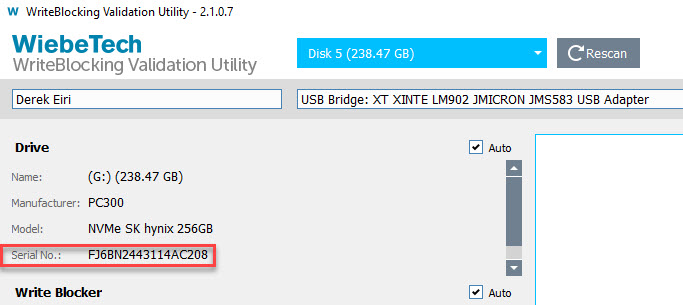
The serial number etched to the case is 3156-A34903. The SK hynix SSD inside is labeled with the serial number FJ6BN2443114AC208.

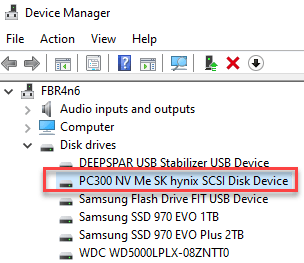
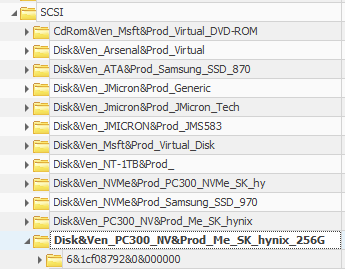
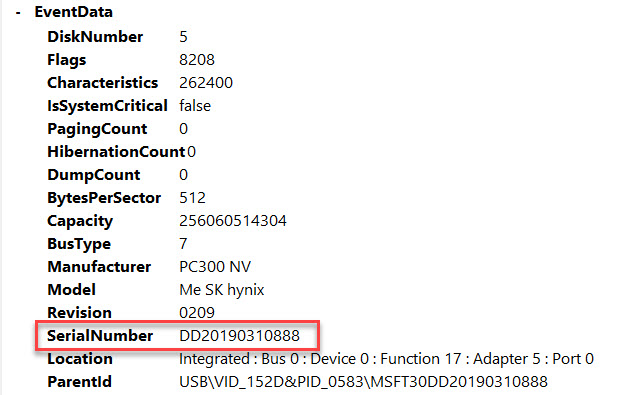
Another enclosure (ENCU3NV-J01, JMircon JMS583) reported numbers other than zeros. Curious, I attached the SK hynix M.2 NVMe SSD to the USB enclosure directly to the computer.
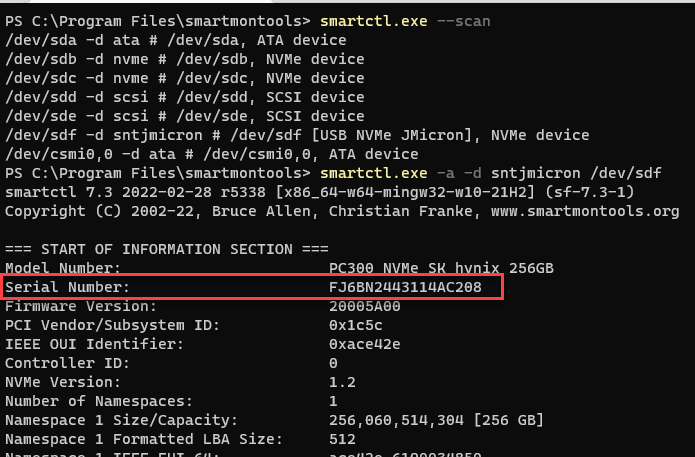
From the Device Manager, its model and manufacturer were listed appropriately. GSmartControl lists the drive as “Unknown”, but the preview was able to display the serial number printed on the SK Hynix SSD’s label. The SYSTEM registry SCSI key for the SSD has a value that includes “&” as the second character. The Microsoft-Windows-Partition/Diagnostic.evtx reports another number that matches the number reported by SAFE Block and Guardonix. With smartctl.exe and the WiebeTech WriteBlocking Utility, the serial number matches the serial number on the SSD.
“No big deal. I can always depend on the drive label!”
Write(r’s) Block Thoughts
Based on what I know today, there is so much more to learn!
The with the primary objective in mind, I believe the write blocker most appropriate for our team’s compact and capable go-bag is the Guardonix Professional with a Plugable USB to M.2 NVMe enclosure using an RL9210 chip, a USB to SATA adapter with power, and a Tableau mSATA/M.2 SATA adapter.
While I’d really like for it to report on an M.2 NVMe SSD’s serial number or other SMART attributes, it may not be critical.
Serial numbers: Almost always, an M.2 NVMe SSD is the system drive of a target machine running a Windows OS. If I needed a sanity check on the serial number, I can review the Microsoft-Windows-Partition/Diagnostic.evtx log, Event ID 1006.
SMART Attributes: After creating a forensic image of the drive, I may be able to check the SMART attributes of the NVMe SSD with a Linux OS via smartmontools. Will this work? What changes will be made? I don’t know, but that’s an experiment for another day. I appreciate how Tetra Defense and Arman Gungor offer information why SMART attributes may be relevant to an investigation.
Alternatively, the Guardonix Professional may be paired with the WiebeTech NVMe WriteBlocker.
On 2023-04-04, I answer my own question about reviewing SMART information from NVMe drives here.
DeepSpar’s New Product
By way of requesting for serial numbers and other SMART attributes from M.2 NVMe SSDs to be reported by Guardonix, Serge Shirobokov shared information about a new DeepSpar product (Stabilizer Pro 10Gb) expected to be released by the end of the year. Based on this information, I think this new product would be an enhanced option for our go-bag.

After years in development, the new DeepSpar device will have 10Gbit hardware and ports for M.2 NVMe, SATA, USB-C, and 2x USB-A. It also has 3 independent channels (A, B, and C) and is capable of working with 3 data sources at the same time.
For example you can image a SATA SSD at 500MBps, a USB flash drive at 300MBps, and a USB HDD at 200+MBps at the same time! The max single channel speed is reported as 800+MBps.
DeepSpar is expecting to release the hardware with the USB Stabilizer Professional firmware by the end of the year and the Guardonix Professional firmware early 2023.
From my perspective, a multi-channel Guardonix with its existing advantages, in a compact package, is more desirable than three independent hardware write blockers for NVMe, SATA, and USB.
Summary
The goal was to evaluate potential write blockers for a go-bag we’re not expected to frequently use in a corporate environment familiar to us. While techniques and equipment for write blocking of most storage types are well known and tested, there are fewer options available for the M.2 NVMe SSD.
I searched for write blockers available that are capable of imaging the storage and interface types we anticipate and created a matrix of the appropriate unit and adapters.
I tested write blockers personally available to me and noted general speed observations and how “serial numbers” are reported by different tools. I also briefly considered how I might verify the serial number of a Windows OS system drive and view SMART attributes for M.2 NVMe SSDs.
There is much to be learned in this area.
Overall, I believe the Guardonix with the Professional firmware is an excellent write blocker for a compact and capable go-bag. I’m crossing my fingers that DeepSpar will add serial number and SMART attribute reporting of M.2 NVMe drives for the Guardonix.
I expect to see vendors and researchers continue to develop digital forensic capabilities and techniques for M.2 NVMe SSDs as utilization increases. I’m especially looking forward to DeepSpar’s new product with improved hardware and greater capability that will undoubtedly be another great tool for the digital forensic investigator on-the-go.
Resources
While not referenced in-line in this post, listed are some resources I found helpful. Do you recommend other links or books I should take a look at regarding storage device standards? Drop them in the comment section below!
Go-bag related:
Beth Jenkin’s At-Scene Guidance Documentation
https://blogs.cisco.com/security/whats-in-your-incident-response-go-bag
https://www.dfir.training/blog/what-s-in-your-dfir-go-bag
https://www.dragos.com/blog/industry-news/preparing-for-industrial-cyber-response-what-to-have-in-your-incident-response-toolkit/
https://sethenoka.com/build-your-own-forensics-go-bag/
Imaging:
https://www.forensicfocus.com/articles/forensic-imaging-of-hard-disk-drives-what-we-thought-we-knew-2/
Write Blockers
https://github.com/msuhanov/Linux-write-blocker/blob/master/research/2017-01_Write_blockers.pdf
SMART Attributes
https://www.youtube.com/watch?v=HTFWWPWRX6A
https://www.forensicfocus.com/articles/smart-anti-forensics/
Updates:
2023-03-19: Updated link for Tetra Defense’s article on using SMART for a case to an archived version at archive.org.
2023-04-04: Added a link answering my own question about retrieving SMART information from NVMe SSDs.


Leave a comment