I am fortunate to be employed at an organization that considers a training budget beyond the allotted tuition reimbursement. I don’t ever expect or take the opportunity for granted, so it’s great news when an opportunity to take a course is offered and approved.
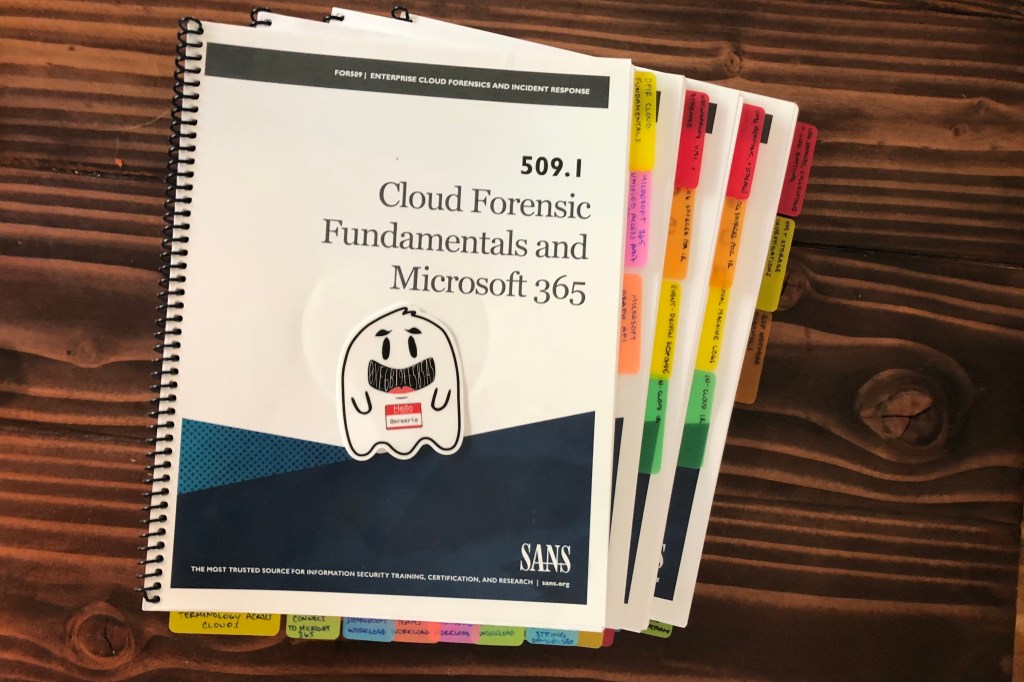
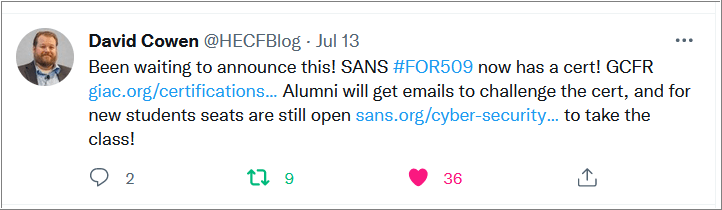
I considered a handful of courses. Among them was FOR509, Enterprise Cloud Forensics and Incident Response, in part due to a tweet by David Cowen.

Several surveys and reports suggest more organizations are migrating from on-premise to cloud environments. The DFIR opportunity is certainly there. Aside some knowledge and interaction with one of the cloud platforms, I don’t have any other experience. Further, there doesn’t appear to be another class like it. This direction (FOR509), for me, made sense.
Cowen reinforced my reasoning in the recorded introduction of the course: “If you’re saying to yourself, ‘Dave, I’m never going to use one of those clouds. My work and projects simply don’t take me there.’ I think you’ll find in the future you might end up there anyway […]. So you need to be prepared.” I like to be prepared.
Based on the 4-day syllabus, I expected the following:
- Sufficient coverage of cloud fundamentals so I may comprehend the related material.
- Sufficient description of each cloud platform’s features and platform specific terminology to be able to understand and communicate with the people who maintain it.
- Concise descriptions of what logs are available and how to analyze them for an incident.
Summary of Thoughts on FOR509
FOR509 (OnDemand) absolutely fulfilled my expectations. In addition to a satisfactory understanding of the relevant logs covered, I perceive that I am better able to analyze new logs as I encounter them. I’ve already cleaned up a SIEM dashboard based on what I learned.
Can you figure it out on your own? Absolutely. A SANS course with configured labs just makes learning efficient. The FOR509 labs will continue to be useful from time to time, as I do the labs from FOR500 and FOR508.
I would recommend this course if you:
- have a strong desire or interest to learn about incident response involving enterprise cloud environments, or
- are an individual with exposure to at least one of the covered cloud providers in an organization with incident response or internal investigation related responsibilities.
I suspect this applies to most SANS courses – I wouldn’t recommend FOR509 if you have no intention of completing the labs and expect to retain any information. I perceive that there is significant value in the lab exercises. This is especially true if exposure to any of the covered cloud providers is limited.
While FOR509 advertises that previous cloud knowledge is not necessary (it’s true), below are some resources that may be helpful to prime you for the course. Previous experience working with a SIEM (also not necessary) is helpful, too.
| Documentation | Relevant Training Resources |
| Microsoft 365 | Microsoft 365 Fundamentals |
| Amazon Web Services | AWS Training and Certification |
| Microsoft Azure | Azure Fundamentals |
| Google Cloud | Google Cloud Skills Boost |
In the updated course, FOR509 includes Google Workspace, Kubernetes forensics and IR, and a capstone challenge. With the rapid changes and updates to the course already baked in, I look forward to taking this course again at a discounted rate. If you took the 4-day course, as I did, SANS has a special offer for alumni to take the entire 6-day course for the price of the last two days. Bonus: The GIAC Cloud Forensics Responder (GCFR) certification is now available.
Megan Roddie will introduce the cloud forensics and IR poster on 08/02/2022, which will undoubtedly help as a reliable and accessible reference.
Having completed the 4-day OnDemand course, Cowen’s preview of the FOR509 6-day course on the SANS Digital Forensics and Incident Response YouTube channel is an accurate representation of what you will learn. I really enjoyed my learning experience with FOR509. I imagine that if you’re reading this blog for information about FOR509, you will enjoy it too.
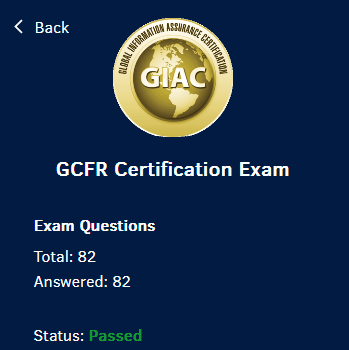
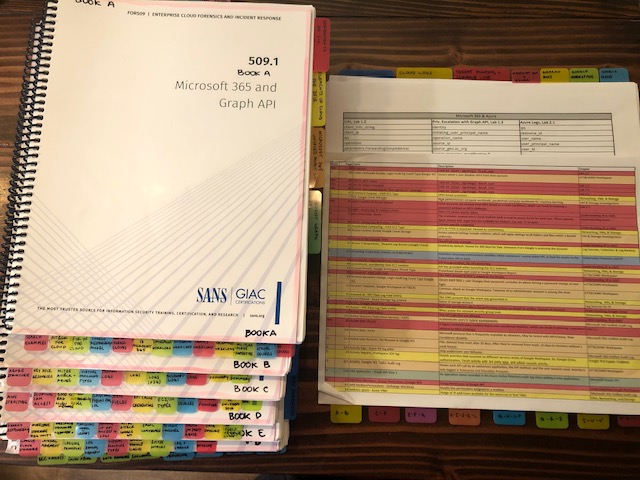
Update, 2023-01-12: Consistent with what Cowen shared, SANS offered the discount to take the 6-day; however, I had until 2022-12-20 to redeem it. Fortunately, tuition reimbursement covered it and I was able to retake the entire course, which included information on Kubernetes and Google Workspace. Having passed the GCFR certification, I offer some universally shared tips when preparing for a GIAC exam:
- After your first read through the material, review the certification objectives. I find this helpful to categorize the information I just read (and will read again) respective to those objectives.
- Understand the exam format, including the minimum passing score. As of 2023-01-12, the GCFR minimum passing score is 62%. If you just want to pass, this might help alleviate any test anxiety you may have.
- Do the labs more than once.
- Read through the material again.
- Create an index.
- Consider creating supplemental material. As I practiced the labs, I made notes of critical log fields.
- Practice Exam #1: I enable the option to show answers and explanations only for incorrect submissions. My goal is to seek holes in my knowledge and index. I use a digital version of the index and supplemental material for easy searching if I struggle to find a keyword. I try to take the first practice exam 10-15 days before exam day.
- I’ll skim through the books and spot-check if it is available in the index.
- Practice Exam #2: I’ll print out what I believe is a solid index in color, including any supplemental material I created. My goal is to simulate the test environment, so I disable the option to show answers and explanations for any submission. If I find more holes in my index, I’ll write them in. I try to take the second practice exam 2 days before the exam. I don’t do anything exam related the day before the exam.
- On the day of, before the exam, I’ll get in a brisk cardio session and go easy on the coffee.
Leave a comment