Some time ago, I read blog posts written by Jason Hale (Digital Forensics Stream) and Sandor Tokesi (Forensix Exchange) on USB device forensics. Of particular interest and value to me, they documented their observations of event ID 1006 in the Microsoft-Windows-Partition/Diagnostic.evtx log. From event ID 1006, device identifiers, connection times, and disconnection times are among the details that may be collected.
That information may be helpful when investigating an allegation of data exfiltration, or to identify a USB device that malware may have originated from.
When reviewing a timeline, I noticed a handful of prefetch files that were modified around event ID 1006 from Microsoft-Windows-Partition/Diagnostic.evtx when a USB drive is attached to a machine. Some organizations may have a Group Policy enabled that deny write access to USB devices not protected by BitLocker, so I wanted to better understand the how the policy impacts the creation or modification of the prefetch files I was observing.
Windows 10 Pro
OS Build 19043.1466
Deny write access to removable drives not protected by BitLocker: Enabled
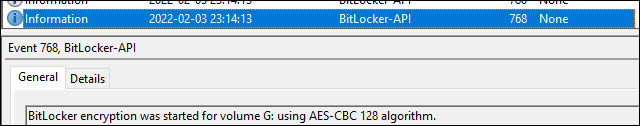
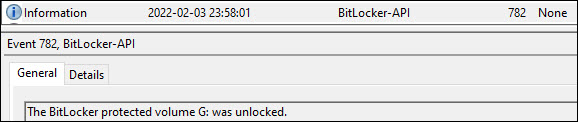
From Microsoft-Windows-BitLocker-API/Management, general information when a BitLocker was enabled on a volume (ID 768), unlocked (ID 782), or reverted to an unprotected stated (ID 778) is available. Prefetch files for FVEPROMPT.EXE, BITLOCKERWIZARD.EXE and FVENOTIFY.EXE appear to be created or modified in the following circumstances:
| Prefetch File Created or Updated | Observation |
| FVEPROMPT.EXE: | If “Deny write access to removable drives not protected by BitLocker” is enabled, a drive not protected by BitLocker is attached to the machine, and a BitLocker prompt appears. |
| BITLOCKERWIZARD.EXE | When a drive is selected to turn on, or manage, BitLocker. Casual note: It appears a prefetch file is created or modified for BITLOCKERWIZARDELEV.EXE when a fixed or OS drive is selected to turn on BitLocker. |
| FVENOTIFY.EXE | A drive with BitLocker not enabled and a process to encrypt it begins; or A drive with BitLocker enabled is attached to the machine, and is unlocked. |
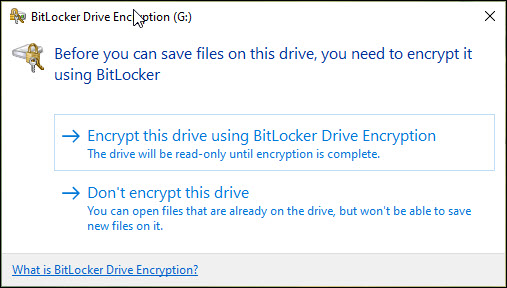
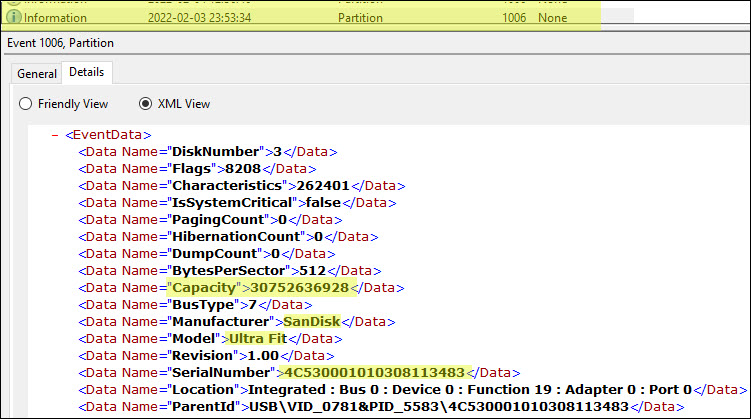
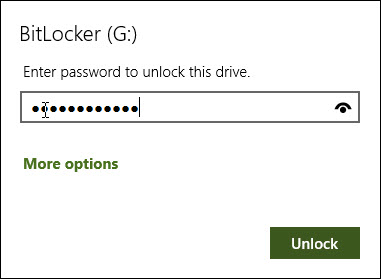
With the Group Policy enabled, I attached a SanDisk Ultra Fit USB flash drive to a personal machine. BitLocker is not enabled. As expected, a prompt is displayed to either encrypt the drive with BitLocker, or use as a read-only drive.
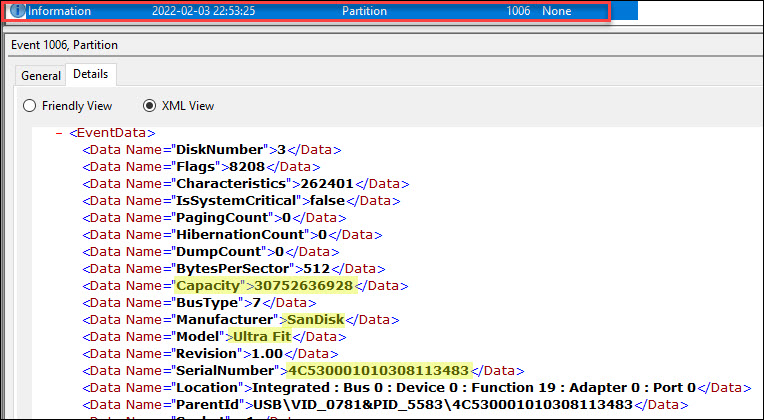
Consistent with my observations, based on information shared by Hale and Tokesi, Microsoft-Windows-Partition/Diagnostic.evtx recorded event ID 1006 on 2022-02-03 at 22:53:25 PST, or 2022-02-04 at 06:53:25 UTC, when the drive is attached to the machine.
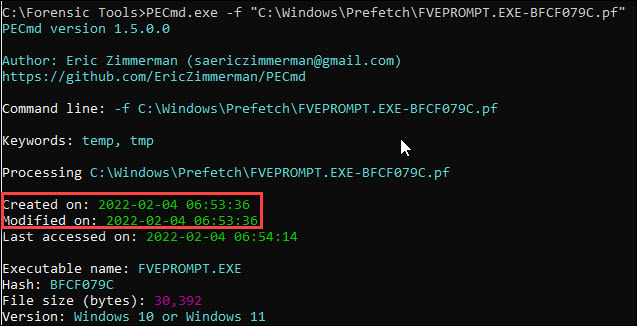
The BitLocker prompt appears associated with the creation or modification date/time of a prefetch file for FVEPROMPT.EXE.
First, I mounted it as read-only. After taking a handful of screenshots, I turned BitLocker on. I selected the following options:
- Save to a file
- Encrypt entire drive
- Compatible mode
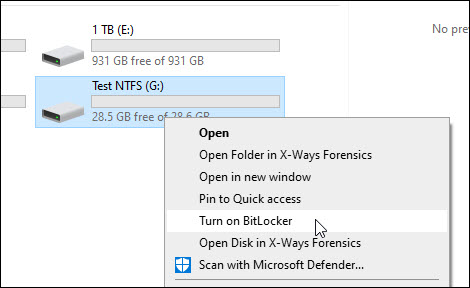
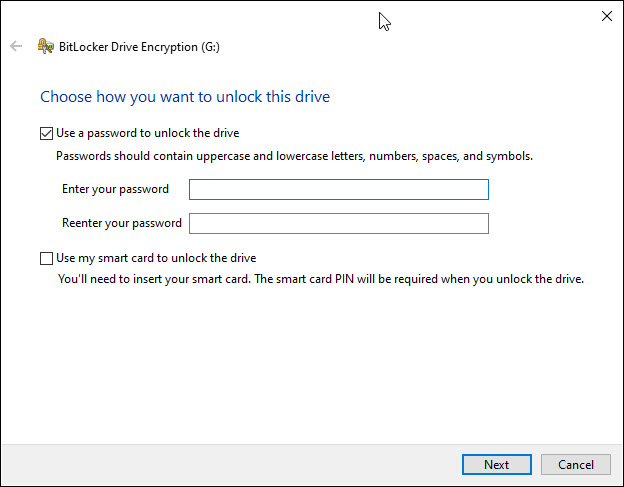
After selecting “Turn on BitLocker” to click through the BitLocker options, it created/modified the prefetch file for BITLOCKERWIZARD.EXE.
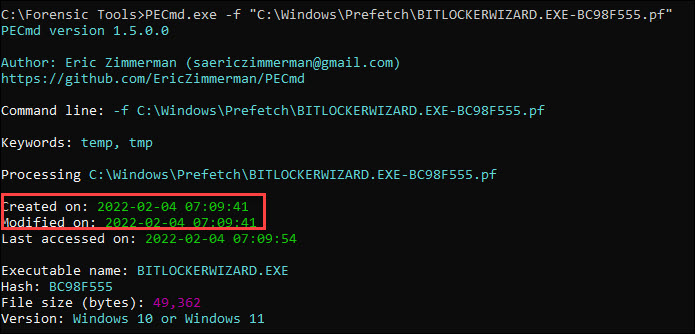
After selecting the BitLocker options, I started the encryption process.
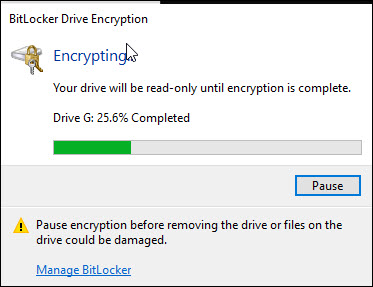
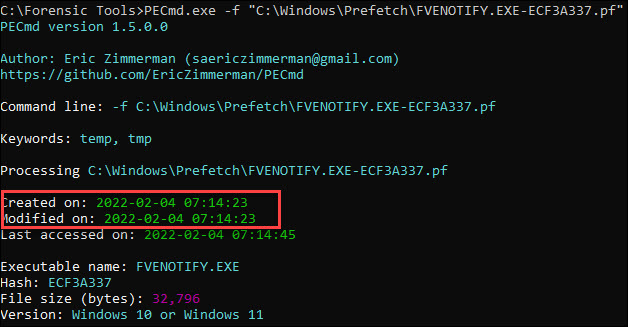
The encryption process created/modified a prefetch file for FVENOTIFY.EXE.
After I removed the USB drive, event ID 1006 was recorded in Microsoft-Windows-Partition/Diagnostic.evtx. USB drive identifying information is recorded, except the “Capacity” value for the event is “0”.

When re-inserting the BitLocker enabled USB drive, prefetch files for BDEUISRV.EXE and BDEUNLOCK.EXE were created or modified in pairs if no action on drive is taken.
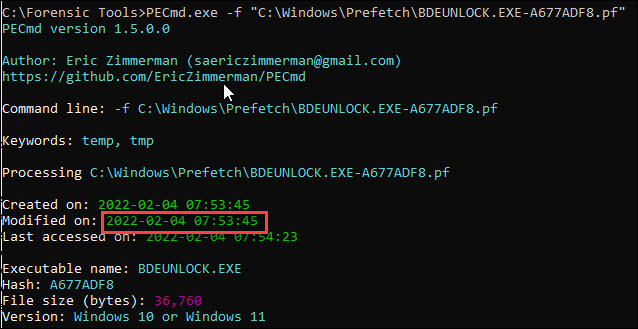
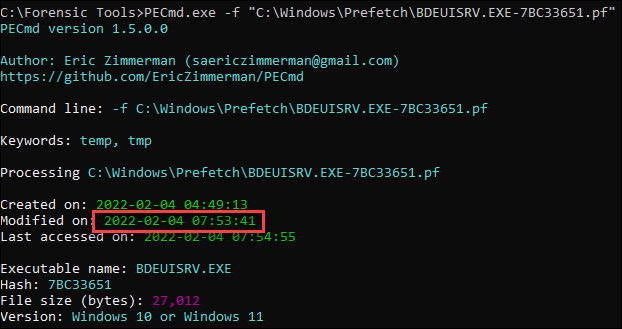
After successfully unlocking the BitLocker enabled USB drive, the prefetch file for FVENOTIFY.EXE and BDEUNLOCK.EXE were created or modified and an event was recorded in Microsoft-Windows-BitLocker-API/Management.


In a USB exfiltration allegation with a wide scope, but in a relatively well-known environment, I imagine looking for evidence of execution of BITLOCKERWIZARD.EXE or FVENOTIFY.EXE may be helpful to narrow down a sample of machines that enabled BitLocker on a drive or decrypted a BitLocker enabled device. This may be especially helpful if most users do not ordinarily have a business need to store data on a USB drive.
Leave a comment