Dell Data Protection Encryption (DDPE) is a file-based encryption method used by organizations to protect data. Processing data protected with DDPE for analysis requires additional steps, i.e., retrieving the encryption key as a .bin file.
Magnet Forensics introduced DDPE support with AXIOM Cyber 6.5 on 2022-09-01 and is briefly described here. Dell’s EnCase Administrator Guide outlines the requirements to retrieve the encryption keys here. While Dell’s guide is intended for Encase, the details described are useful to inform on the overall process.
In short, three values associated with the target computer protected with DDPE is required to retrieve a valid key file from the organization’s Dell server to decrypt the files:
- Shield ID (aka Device ID, DCID, Recovery ID, or SCID)
- Machine ID (aka MCID, Unique ID or host name)
- Dell Server URI
If the host name is known, the Dell server may be queried for the remaining two values to download the key file.
However, if a pile of storage media likely using DDPE is discovered without any documentation – hope is not lost. All three values may exist in registry hive.
| Shield ID is the DCID registry value | HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\CMGShield |
| Machine ID is the MCID registry value | HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\CMGShield |
| Dell Server URI | HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\CMGShield\Servlet |
It’s easy enough to traverse the registry, but I wanted to explore a couple of other methods to retrieve this information.
Create a Registry Report Definition File for X-Ways Forensics
XWF has several report definition files that exist out-of-the-directory and may be modified as needed. Alternatively, a new definition file may be created for a specific task, i.e., pull the three values from the SOFTWARE registry key to decrypt DDPE protected files. The definition file “Reg Report ddpe” was created using the specifications described in the manual (section 5.9).
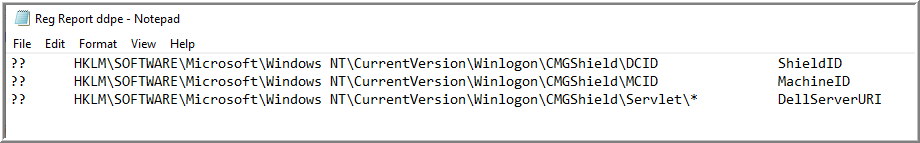
| ?? | Definition for any Windows version |
| HKLM\SOFTWARE\[…] | Full path of registry keys |
| * | Lists all keys on the same level and deeper in the report |
| ShieldID, etc. | Description included in the report |
The HTML report generated will have four columns: description, extracted value, registry path as a tool tip, and last modification date of the corresponding key. I found this to be a very simple way to print out specific registry values using existing XWF functionality.

Create and Submit a RegRipper Plugin
I thought it would be great if I could run Harlan Carvey’s RegRipper against a mounted volume and its respective SOFTWARE registry key. However, I needed to create the plugin first.
I don’t have a background in Perl and it turns out I didn’t need to. If the only requirement is a handful of registry values, several plugins that exist in the GitHub repository may be used as a template. To get a feel for the syntax, I found it helpful to review plugins for registry artifacts I’m familiar with. After a few moments of time and testing, I had an operational plugin.
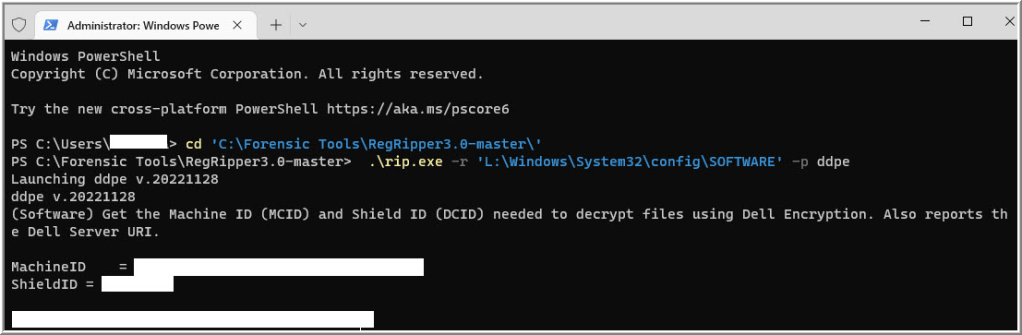
Satisfied, I saved it in a common area where my colleagues have access to it. As I was about to share where to access the plugin with my colleagues, I realized how silly that was.
Instead, I submitted a pull request. It is now included with RegRipper and the plugin will be there every time it is downloaded. Bonus: including it in the repository accounts for two of the three value propositions for RegRipper described by Carvey.
Summary
I briefly describe DDPE and important values required to decrypt files it protects. Some of these values may be retrieved from registry hive by navigating to their respective paths. Optionally, they may be retrieved by creating a registry report in X-Ways Forensics or using a RegRipper plugin.
The XWF registry report definition file to retrieve relevant DDPE registry value data may be found here.
The ddpe.pl plugin to retrieve relevant DDPE registry value data is included in RegRipper here.
Related links/resources I found helpful while writing this blog post:
From Registry With Love: Malware Registry Abuses, Splunk Threat Research Team
RegRipper, Brett Shavers
Why I like Perl for Forensic Analysis, Harlan Carvey
X-Ways Practitioner’s Guide 2E (Chapter 7), Brett Shavers
Leave a comment