Ordinarily, X-Ways Forensics is capable of exploring archives. The details of this capability is documented in the manual, section 6.3.4.
I encountered a 7Z archive that I was not able to explore, despite knowing the password. After entering a known, valid, password, the decryption window would continue to popup.

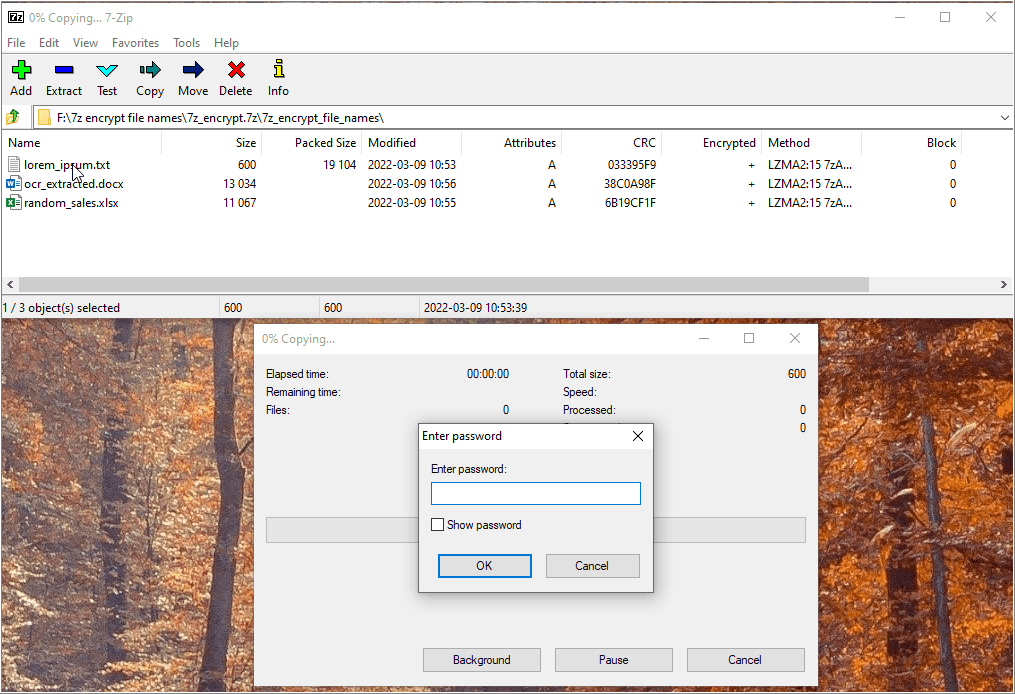
To assure myself the archive’s password does work, I used an associated viewer program to open the archive with 7-Zip File Manager. I was able to validate that the password is correct, and view the archive’s contents.

When I attempted to open the archive via Windows explorer, a file list of the archive was not available. Ah ha. This consistent for encrypted archives created with “Encrypt file names” enabled.

The manual explicitly states that “RAR archives and 7Z archives in which not only the file contents, but also the names are encrypted are not currently supported.” Therefore, my initial observation of not being able to explore the archive within XWF is expected. Perhaps it may be supported in the future.
Applicable Lessons
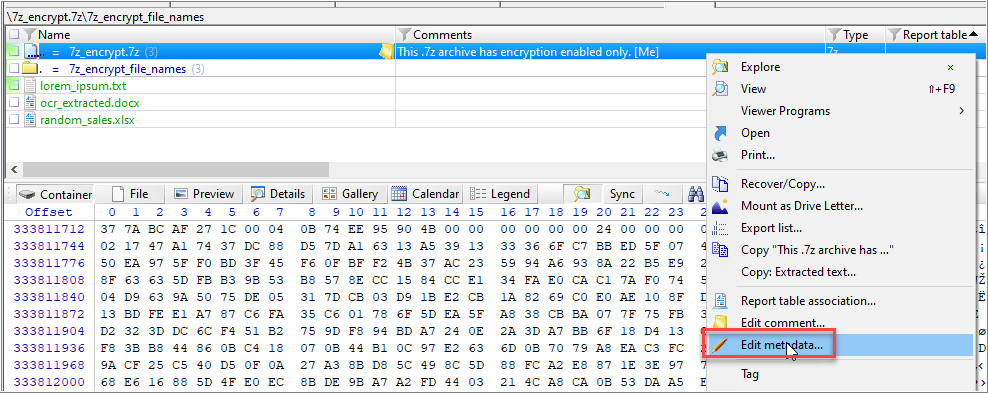
After refining a volume snapshot, XWF may log notable events. These logged events may provide context, in the form of an automatically generated report table, for certain files that may warrant further examination (5.7, Report Tables). For this example, a report table, “Unable to explore,” was associated for the file, “7z_encrypt_file_names.7z.” This makes sense as it is known the file names are encrypted, too.


To review these types of archives, the report table column may be filtered for “Unable to explore”. Additional filtering for items with the attribute, “e!” may be helpful.
To open the archive outside XWF, there are options:
- The archive may then be saved outside of XWF (Recover/Copy). The contents may be extracted with 7-Zip File Manager program from Windows explorer.
- The volume/evidence file container may be mounted as a drive letter (5.16, Mount As Drive Letter). Extract the contents with 7-Zip File Manager. The contents may be extracted with 7-Zip File Manager program from Windows explorer.
- The Directory Browser’s context menu may also used to open the encrypted archive with file name encryption with an associated program (Viewer Programs | Associated Program).

For encrypted archives without file name encryption enabled, the known password may be entered manually by editing the metadata from the Directory Browser’s context menu (6.3.4, Archive Exploration). With this method, XWF is able to explore the archive internally.

I’m glad I read the manual.
- Brian Carrier, File System Forensic Analysis (Upper Saddle River, NJ: Addison-Wesely, 2005), 360-361.
Leave a comment