On page 138 of the X-Ways Forensics/WinHex Manual (Updated 2021-12-31), it states:
X-Ways Forensics can extract specific data from the event payload in .evtx event logs and list them directly in the event list.
The definition file, Event Log Events.txt, may be configured. It’s only a matter of listing the individual data fields to extract, and verifying that it works.
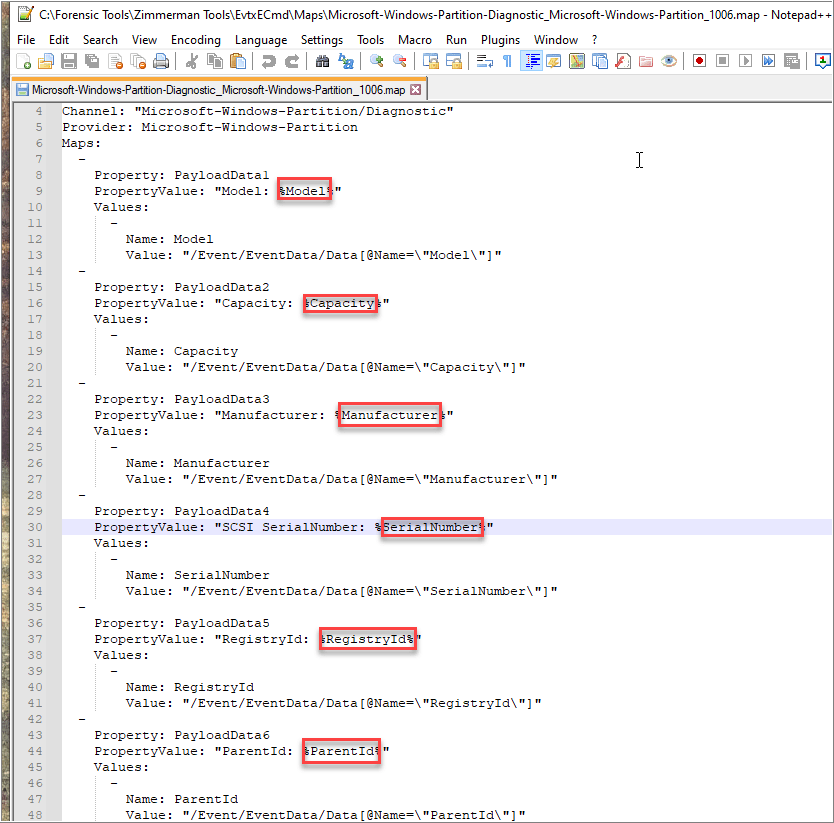
While exploring X-Ways Forensics’ events list feature for a previous blog post where I briefly mentioned event ID 1006 from Microsoft-Windows-Partition/Diagnostic, I noted that the output was sparse. I wanted to try and populate the description column with additional information.

I remembered that Eric Zimmerman’s EvtxECmd already has the most pertinent fields mapped out, so I just used that to reference which fields I wanted to pull.
To extract specific fields, start with X-Ways Forensics’ default definition file, Event Log Events.txt. If in doubt, start again with a fresh manual installation of X-Ways Forensics. Then add a new row, while retaining the tab delimiters.
EventID <tab> optional log provider <tab> datafield1,datafield2,datafield3

If <Event data> is available, X-Ways Forensics will parse it when refining a volume snapshot (RVS).


Considerations:
During my initial attempts to extract fields, I was inadvertently adding quotation marks in the .txt definition file. I recently learned the parser will not work correctly if it does.
Quotation marks would appear in the .txt file when viewing it in a text-editor after the following sequence:
1) Opening the default tab-separated .txt file in MS Excel.
2) Save file.
After some searching, MS Excel adds the quotation marks around the extracted fields because the comma in CSV files may represent it as delimiter. The quotes are used as text qualifiers.
While quotation marks are OK for File Type Signatures *.txt, it is not for Event Log Events.txt.
Edit, 06/08/2022: While I am able to parse <Event data> that XWF was able to process, it does not appear to be complete when compared to EvtxECmd. With the same file, EvtxECmd.exe is able to map out 24, 1006 event IDs with the map that it is packaged with. XWF, as of v20.5 SR-2, processes 8 of the 24.
Edit, 11/11/2022: With the release of 20.6 SR-5, X-Ways made improvements with how it processes Windows event logs. I’m now able to extract all 24 rows. Also for consideration, when creating entries in the Event Event log file, “Provider Name entries should not contain anything from (and including) the forward-slash. For example, “Microsoft-Windows-Bits-Client/Operational” should be “Microsoft-Windows-Bits-Client”.”
Very large data associated with in Windows event logs events previously were not output at all and caused malformed lines in the TSV representation. That was improved. Up to 8 KB of that data are now included.
20.6 SR-5 Update

Leave a comment